Collection Satellites and Imagery Intelligence Explained

Imagery intelligence is any form of intelligence that shows us what’s going on with images. Most commonly it comes in the form of satellite photography though these days it could include unmanned aerial vehicles (UAV). Imagery can include a variety of products such as terrain mapping, area monitoring. Just think of Google Maps on steroids. There are also a variety of modes that can be used such as thermal or infrared imaging. Depending on what’s going on, leaders on the ground may be able to request real-time overhead reconnaissance of the area ahead of them. A UAV will actually have a live action camera feed that will be sent back to the tactical operations center and the information can be relayed to the battlefield commander before they walk into an IED or ambush.
A UAV will usually have a specific flight pattern which may take it along main supply routes commonly used by coalition forces, or it may just fly around an area of responsibility providing early warning for anything approaching friendly forces. Satellites are a little harder to request because of the limited number available and the high priority requests that are waiting in line to get their product at any given time. And for some of the higher priority areas or hot-spots, a satellite will stay in geosynchronous orbit essentially hovering over a certain spot on the earth’s surface making it unavailable for many other taskings.
UAVs have actually recently been compromised by Iraqi insurgents, mitigating the advantage they gave us and leveling the playing field by making the same information available to them. One of the reasons that our imagery capabilities are so closely guarded is because we don’t want to compromise our ways and means or technical capabilities. Think about it, if you could tell where a picture was taken from based on the angle and perspective and you wanted to hide what you were doing as part of a counterintelligence or operational security posture, you would know how to go about concealing it. For example, if you have nosey neighbors you may choose to grow a 6-foot hedge around your property. If you discovered a peeping tom, you may ensure that all blinds remain closed. If you have a psycho-stalker ex- you may use blinds and then put lights near the windows so as not to cast shadows on the blinds so that they don’t know how many people are in the house or which rooms have someone in them.

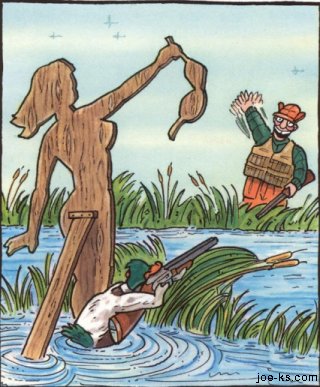
Deception
For those of us that remember the movie Home Alone in which Kevin rigged his house to look like there was a full blown Christmas party going on. In the real world, there are a number of methods used to deceive the enemy’s imagery collection assets. In WWII, there were many decoy aircraft and decoy sites constructed just for show to provide enemy analysts with false information to draw inaccurate conclusions. In fact because having a bunch of equipment that would normally be camouflaged out in the open, they were able to set up decoy aircraft and vehicles, and then leave only a few with poor camouflage perhaps a tank barrel or propeller would be left partially exposed. so that it looked like everything else was still there and hidden from view. Once this was done, the same decoys would be taken to another location and the process repeated. (Owen 2002, 137). This tactic was very effective at preventing the enemy from discerning the true strength of forces which of course effected their analysis and ability to react to the reality.
There was however, one time that imagery really saved us, the Cuban Missile Crisis.
A great grab bag of intel and espionage